News
The Rise of Data Extortion: Why Paying the Ransom Won’t End the Threat
Think ransomware is the biggest threat to your business? It’s not anymore.
Hackers have stopped playing by the old rules. Instead of encrypting your files and demanding payment for the decryption key, many are skipping that step entirely. Now, they’re just stealing your sensitive data and threatening to leak it publicly if you don’t pay up.
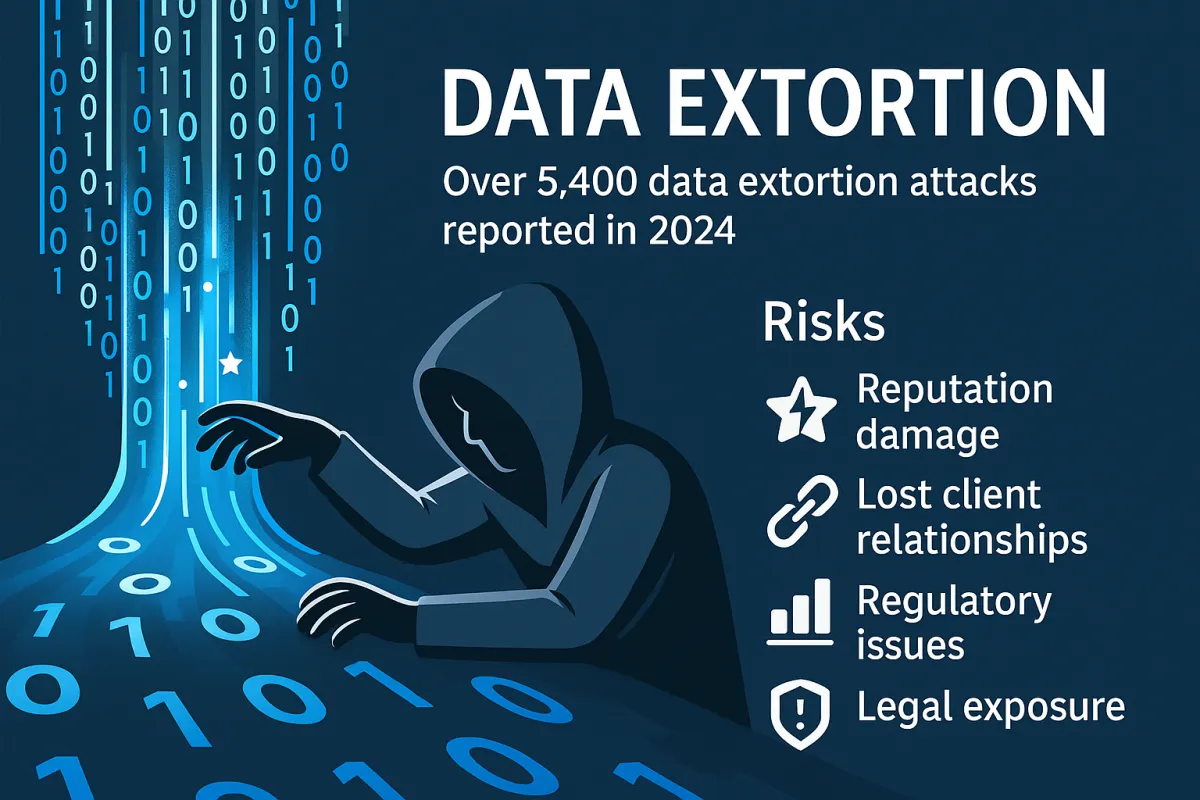
It’s called data extortion, and it’s spreading fast. In 2024, over 5,400 of these attacks were reported around the world—an 11% increase in just one year.
If you think your firewalls and antivirus software are enough to stop it, you’re already behind.
What Is Data Extortion?
Unlike traditional ransomware attacks that lock you out of your files, data extortion skips the encryption altogether. Here’s the playbook:
Hackers gain access to your systems, often through stolen credentials or unprotected remote access.
They steal confidential data: client records, employee files, financial info, and intellectual property.
Then they threaten to publish it unless you pay—sometimes even if you do.
This approach is faster, sneakier, and harder to detect than traditional ransomware, and it puts even more pressure on business owners like you.
Why This Is More Dangerous Than Encryption-Based Ransomware
Data extortion hits where it hurts most: your reputation, your relationships, and your compliance.
Reputation Damage: If client or employee data leaks, trust evaporates. And you can’t buy that back.
Compliance Violations: A breach can trigger HIPAA, GDPR, or other regulatory penalties.
Lawsuits and Legal Exposure: Clients, employees, and even vendors may sue you for negligence.
No End in Sight: Hackers can re-extort you months or even years later using the same stolen data.
This isn’t just a tech problem—it’s a business risk. And if you’re not prepared, you could be left exposed.
Why Hackers Are Skipping Encryption and Going Straight for the Data
Encryption takes time. Stealing and threatening to leak your data? That’s quick, profitable, and easier to hide from traditional cybersecurity tools.
Faster payouts = more victims, more profit.
Harder to detect = fewer alarms triggered.
More pressure to pay = greater emotional and legal consequences.
And with AI in their toolkits, hackers can now automate much of this process—including identifying what data to steal and how to weaponize it.
Why Your Current Cybersecurity May Not Be Enough
If you’re relying on basic antivirus or a firewall, you're vulnerable. Most traditional tools are designed to stop ransomware—not data theft.
Hackers today are:
Using info-stealing malware to harvest credentials
Exploiting cloud storage misconfigurations
Disguising data theft as regular network activity
You won’t see it coming until the extortion email lands in your inbox.
What You Can Do to Protect Your Business
It’s time to upgrade your approach to cybersecurity. Here’s where to start:
Adopt a Zero Trust Framework
No one gets in automatically. Verify every user and device.
Use multi-factor authentication (MFA) across the board.
Invest in Real-Time Threat Detection and Data Loss Prevention (DLP)
Monitor for unusual data activity.
Block unauthorized file transfers.
Watch your cloud environments, not just your office network.
Encrypt Everything
If your data is encrypted before it’s stolen, it’s useless to hackers.
Build a Backup and Recovery Strategy
Keep offline backups.
Test your recovery plans regularly.
Train Your Team
Human error is still the #1 cause of breaches.
Teach your team to recognize phishing and follow smart security habits.
Don’t Let a Hacker Set the Terms of Your Next Crisis
Data extortion isn’t some distant threat—it’s already happening. And it’s targeting businesses just like yours.
At qnectU, we help business owners take back control by building cybersecurity strategies that work in the real world. Strategies that stop threats before they hit and help you sleep better at night, knowing your business is protected.
Let us identify your current vulnerabilities and show you exactly what needs to be fixed. Simply click here to schedule a quick 26-minute call before it’s too late.
Because today’s hackers don’t play fair—and your defense strategy shouldn’t be stuck in 2020.
FREE GUIDE
Discover The Truth Nobody Is Telling You About IT Security And The New, Critical Threats That WILL Put Your Business At Risk
I Consent to Receive Notifications, Alerts, and Communications from the company. Message frequency varies. You can reply STOP to unsubscribe at any time.
Answers To Common Questions
Frequently Asked Questions
Do you offer access to senior IT consultants or a vCSO for oversight and guidance?
Yes, we offer access to senior IT consultants and provide vCSO(Virtual Chief Security Officer) as a service for our clients. Our vCSO service provides your organization with expert leadership and strategic direction tailored to your unique cybersecurity and legal compliance needs. We are here to help you navigate the complexities of cybersecurity and ensure that your security posture is robust, compliant, and capable of addressing evolving cyber threats. Book a call today to get expert help with your company’s cybersecurity and compliance.
Do you have a high level of confidence in your security posture? If so, can you explain why?
We have a high level of confidence in the security posture of our company and our clients. Our security stack includes several components to ensure strong and resilient cybersecurity measures. We provide comprehensive risk management, regular audits and assessments, advanced security technologies, employee training and awareness, and incident response planning. Our systems and solutions follow established industry standards and best practices to keep your company safe and your data secure. Since every company has different risks depending on the data, systems, utilization, and more, we can work with your team to develop a robust security plan and implement the proper measures as needed. Reach out today to strengthen your company’s security posture!
Do you have a Disaster Recovery (DR) plan? If so, what’s in place? Is it tested regularly?
We provide robust Disaster Recovery (DR) plans, covering preventative, detective, and corrective measures. Our DR strategies are tailored to each client’s specific needs and are designed to ensure rapid recovery and continuity of operations in the event of any disaster. These plans are regularly reviewed and tested to guarantee they function effectively and meet the highest standards of resilience and reliability. And if a disaster were to occur outside of regular business hours, we have you covered! At qnectU, we have a response time of mere minutes for emergency after-hours calls, ensuring a rapid response to implement your Disaster Recovery plan. Book a call today to protect your company in the event of a disaster.
Do you perform regular risk assessments?
Here at qnectU, we conduct regular risk assessments as a core part of our risk management strategy. Our process is comprehensive, involving identification, categorization, and response planning for potential security risks, including technical vulnerabilities, access controls, and more. These assessments help us understand, control, and mitigate all forms of cyber risk, ensuring that our security measures are effective and up-to-date. But most importantly, we provide continual risk assessments at pre-determined intervals based on your company’s risk level. This ensures that issues are corrected, new risks are identified, and compliance is properly documented. Want to see how our in-depth business risk assessments work? Book a consultation today to get an in-depth risk assessment of your company’s current network security.
Do you follow proven change management principles?
We are committed to following proven change management principles. We understand the importance of structured and systematic processes in implementing changes that affect cybersecurity protocols and IT environments. Our approach is based on industry-recognized frameworks and methodologies that ensure changes are managed effectively, focusing on minimizing risks, enhancing security posture, and achieving strategic objectives.
Do you address all my compliance needs, including HIPAA?
We specialize in Compliance as a Service (CaaS), and our program is designed to meet a wide range of regulatory requirements to ensure that your business adheres to the highest standards of compliance. We demonstrate our compliance through detailed assessments, documentation, and third-party audits. Our expertise and ongoing support can give you confidence that your company’s sensitive information is managed securely and in full compliance with all regulations.
Is third-party auditing provided to ensure cybersecurity and compliance requirements are being met?
In today’s world a business can easily be compromised via a “supply chain hack.” There have been several instances where the IT company has exposed all of their clients to hacking due to their own lack of cybersecurity measures. In order to prevent this within our own company, we work closely with a third party for comprehensive auditing services to ensure that all cybersecurity and compliance requirements are met. Our rigorous audit process involves a thorough examination of our systems and practices against established industry standards and best practices. This collaboration provides an objective perspective and deep expertise to identify any potential vulnerabilities, ensuring that our cybersecurity measures are robust, up-to-date, and in full compliance with regulatory demands.
What is Compliance as a Service (Caas)?
Compliance as a Service (Caas) means that our experts will give you specialized help in handling all the rules and regulations your business needs to follow. We do this by providing expert guidance to help you determine what rules apply to your business and how to follow them. All while giving ongoing support to monitor your compliance status and updates in regulations. This may also include any advanced tools to help manage compliance tasks and risk management surrounding compliance. CaaS takes the hassle out of compliance so you can focus on running your business with confidence.
Who is Greg Mauer?
Gregory Mauer is the founder and CEO of our company, a best-selling author, speaker, and a cybersecurity & compliance expert. He has been on stage with the likes of the “Nice Shark”, Robert Herjavec, Siri co-founder Adam Cheyer, and business coach and author Mike Michalowicz.
Answers To Common Questions
Frequently Asked Questions
Do you offer access to senior IT consultants or a vCSO for oversight and guidance?
Yes, we offer access to senior IT consultants and provide vCSO(Virtual Chief Security Officer) as a service for our clients. Our vCSO service provides your organization with expert leadership and strategic direction tailored to your unique cybersecurity and legal compliance needs. We are here to help you navigate the complexities of cybersecurity and ensure that your security posture is robust, compliant, and capable of addressing evolving cyber threats. Book a call today to get expert help with your company’s cybersecurity and compliance.
Do you have a high level of confidence in your security posture? If so, can you explain why?
We have a high level of confidence in the security posture of our company and our clients. Our security stack includes several components to ensure strong and resilient cybersecurity measures. We provide comprehensive risk management, regular audits and assessments, advanced security technologies, employee training and awareness, and incident response planning. Our systems and solutions follow established industry standards and best practices to keep your company safe and your data secure. Since every company has different risks depending on the data, systems, utilization, and more, we can work with your team to develop a robust security plan and implement the proper measures as needed. Reach out today to strengthen your company’s security posture!
Do you have a Disaster Recovery (DR) plan? If so, what’s in place? Is it tested regularly?
We provide robust Disaster Recovery (DR) plans, covering preventative, detective, and corrective measures. Our DR strategies are tailored to each client’s specific needs and are designed to ensure rapid recovery and continuity of operations in the event of any disaster. These plans are regularly reviewed and tested to guarantee they function effectively and meet the highest standards of resilience and reliability. And if a disaster were to occur outside of regular business hours, we have you covered! At qnectU, we have a response time of mere minutes for emergency after-hours calls, ensuring a rapid response to implement your Disaster Recovery plan. Book a call today to protect your company in the event of a disaster.
Do you perform regular risk assessments?
Here at qnectU, we conduct regular risk assessments as a core part of our risk management strategy. Our process is comprehensive, involving identification, categorization, and response planning for potential security risks, including technical vulnerabilities, access controls, and more. These assessments help us understand, control, and mitigate all forms of cyber risk, ensuring that our security measures are effective and up-to-date. But most importantly, we provide continual risk assessments at pre-determined intervals based on your company’s risk level. This ensures that issues are corrected, new risks are identified, and compliance is properly documented. Want to see how our in-depth business risk assessments work? Book a consultation today to get an in-depth risk assessment of your company’s current network security.
Do you follow proven change management principles?
We are committed to following proven change management principles. We understand the importance of structured and systematic processes in implementing changes that affect cybersecurity protocols and IT environments. Our approach is based on industry-recognized frameworks and methodologies that ensure changes are managed effectively, focusing on minimizing risks, enhancing security posture, and achieving strategic objectives.
Do you address all my compliance needs, including HIPAA?
We specialize in Compliance as a Service (CaaS), and our program is designed to meet a wide range of regulatory requirements to ensure that your business adheres to the highest standards of compliance. We demonstrate our compliance through detailed assessments, documentation, and third-party audits. Our expertise and ongoing support can give you confidence that your company’s sensitive information is managed securely and in full compliance with all regulations.
Is third-party auditing provided to ensure cybersecurity and compliance requirements are being met?
In today’s world a business can easily be compromised via a “supply chain hack.” There have been several instances where the IT company has exposed all of their clients to hacking due to their own lack of cybersecurity measures. In order to prevent this within our own company, we work closely with a third party for comprehensive auditing services to ensure that all cybersecurity and compliance requirements are met. Our rigorous audit process involves a thorough examination of our systems and practices against established industry standards and best practices. This collaboration provides an objective perspective and deep expertise to identify any potential vulnerabilities, ensuring that our cybersecurity measures are robust, up-to-date, and in full compliance with regulatory demands.
What is Compliance as a Service (Caas)?
Compliance as a Service (Caas) means that our experts will give you specialized help in handling all the rules and regulations your business needs to follow. We do this by providing expert guidance to help you determine what rules apply to your business and how to follow them. All while giving ongoing support to monitor your compliance status and updates in regulations. This may also include any advanced tools to help manage compliance tasks and risk management surrounding compliance. CaaS takes the hassle out of compliance so you can focus on running your business with confidence.
Who is Greg Mauer?
Gregory Mauer is the founder and CEO of our company, a best-selling author, speaker, and a cybersecurity & compliance expert. He has been on stage with the likes of the “Nice Shark”, Robert Herjavec, Siri co-founder Adam Cheyer, and business coach and author Mike Michalowicz.